High Performance
Software Defined
All-Flash Storage
Ultra Low Latency
High Availability
High IOPS
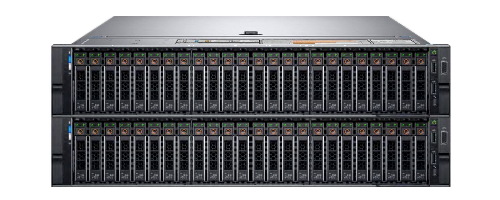
Off-the-shelf Hardware
Flexible Licensing
High Performance
Software Defined
All-Flash Storage
Blockbridge offers ultra-fast and reliable data storage using standard NVMe servers. Get the best price-performance on the market and avoid being locked into expensive and proprietary hardware.
Your Needs
Complete Solutions
Latest News
Announcing: Release 6.0
BLOCKBRIDGE SOFTWARE VERSION 6.0 RELEASE NOTES We’re excited to announce the arrival of NVMe-over-TCP support for the Blockbridge data engine! This project has been a true labor of love for the entire team here [...]
Announcing: Release 5.1
BLOCKBRIDGE SOFTWARE VERSION 5.1 RELEASE NOTES Blockbridge Version 5.1 updates the widely deployed 5.x AnyScale architecture. This release brings numerous performance and stability improvements alongside support for Proxmox, multi-cloud Openstack deployments, Grafana, and an [...]
Announcing: Release 5.0
BLOCKBRIDGE SOFTWARE VERSION 5.0 RELEASE NOTES Blockbridge Version 5.0 is the second major release of the AnyScale architecture. The major feature of this release is Multi-Complex. Multi-Complex Multi-Complex provides in-the-box performance scalability designed to [...]